The NSA Probably Has Installed a Virus on Your Computer — and Everyone Else's
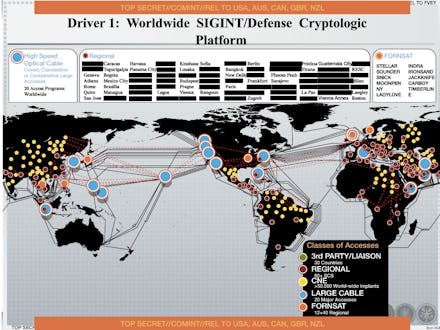
The news: According to yet another National Security Agency (NSA) slide hidden among the treasure trove of documents leaked by Edward Snowden, the NSA has infected upwards of 50,000 computer networks worldwide with malware in an attempt to riddle the internet with hidden access points accessible by U.S. agents.
A presentation from 2012 examined by Dutch news outlet NRC explained the backdoor method in which the NSA collects information worldwide. It uses "Computer Network Exploitation" (CNE), or in other words, massive malware attacks, to secretly infiltrate tens of thousands of networks. According to the NRC, one such scheme was unmasked in Belgium in September. Foreign intelligence agents in the British intelligence service (GCHQ) were revealed to have gained access to telecom provider Belgacom by tricking its employees into visiting a fake Linkedin page.
Translated from Dutch by CNET:
"The American intelligence service -- NSA -- infected more than 50,000 computer networks worldwide with malicious software designed to steal sensitive information.
"Documents provided by former NSA employee Edward Snowden and seen by this newspaper, prove this.
"(...) The NSA declined to comment and referred to the US Government. A government spokesperson states that any disclosure of classified material is harmful to our national security."
The background: The NSA's hacking missions are handled by a special division with over 1,000 hackers named the TAO (Tailored Access Operations). The Washington Post estimated based on secret budget reports that by 2008, the unit had successfully infiltrated over 20,000 networks. By mid-2012 that number had grown to 50,000 and presumably has continued to expand to this day.
According to the Post profile, the TAO is a "highly secret but incredibly important NSA program that collects intelligence about foreign targets by hacking into their computers, stealing data, and monitoring communications." It's also supposedly integral to the development of complex programs that could destroy or damage foreign computer systems following an order from the commander-in-chief.
These kind of cyber attacks don't just bring down computer systems — much like the disastrous incident in Jurassic Park, they can have catastrophic real-world effects by ordering hardware components and infrastructure controlled by the network to malfunction or operate against programming constraints. Stuxnet, a virus which infected Iran's Natanz nuclear facility, was designed to attack uranium enrichment centrifuges and gradually cause serious damage to the equipment over time (even though it was capable of causing a single catastrophic failure at any one point).
The Post found that for all the supposed secrecy, some NSA employees were relatively cavalier on their Linkedin profiles:
"For instance, Brendan Conlon, whose page lists him as a former Deputy Chief of Integrated Cyber Operations for the NSA and former Chief of TAO in Hawaii, says that he led "a large group of joint service NSA civilians and contractors in executing Computer Network Exploitation (CNE) operations against target networks." Barbara Hunt, who is listed as a former Director of Capabilities at TAO in Fort Meade, similarly claims she was 'responsible for end-to-end development and capability delivery to build a versatile computer network exploitation effort.'
"Dean Schyvincht, who claims to currently be a TAO Senior Computer Network Operator in Texas, might reveal the most about the scope of TAO activities. He says the 14 personnel under his management have completed 'over 54,000 Global Network Exploitation (GNE) operations in support of national intelligence agency requirements.' Just imagine how productive the team in Fort Meade, rumored to have about 600 people, must be."
What does this all mean for you? Well, it means that NSA surveillance of the world-wide internet is even more sophisticated and widespread than the average observer might have concluded. For better or for worse, it looks like the NSA has infiltrated large numbers of telecom services, ISPs, financial institutions, and other organizations worldwide that would allow it to gain access to large amounts of data for bulk collection.
The NSA isn't alone in hacking the world; in early 2013, security company Mandiant exposed a Chinese group called Advanced Persistent Threat 1 which they claimed had been responsible for hundreds of attacks against Western targets and requiring a support staff of hundreds.
And some experts warn that mass NSA infiltration of other networks comes with a price. The Electronic Frontier Foundation writes that by secretly introducing vulnerabilities into the world's internet infrastructure, the NSA risks allowing anyone who discovers those vulnerabilities to obtain immense power to bypass the security restrictions which keep the internet safe and reliable.