Hackers stole credit card information from Trump hotel guests for the third time in three years
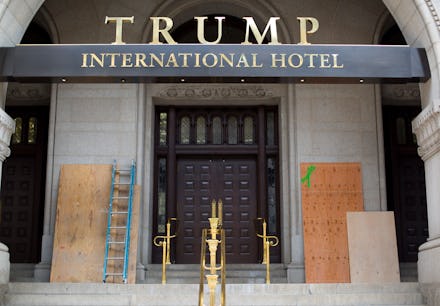
If you’ve recently stayed in a Trump hotel you may want to check your credit card statement for fraudulent charges.
According to the Washington Post, guests at 14 separate Trump properties have had their credit card information exposed. It’s the third time in three years that a credit card scam has affected customers of Trump hotels, the Washington Post reported. The first time occurred in May 2014, when hackers installed malware onto Trump hotels’ payment processing system, the Post reported.
“We recently learned of an incident involving unauthorized access to guest information associated with certain hotel reservations,” a notice on the Trump Hotels website said. “This incident occurred on the systems of Sabre Hospitality Solutions (Sabre), a service provider used by Trump Hotels.”
The notice explained that the breach did not affect Trump Hotels’ systems, but rather affected the Sabre SynXis Central Reservations system, which facilitates the booking of hotel reservations made by consumers through hotels, online travel agencies and similar booking services.
“The privacy and protection of our guests’ information is a matter we take very seriously, and we recommend that affected guests review the information in this letter for some steps they can take to protect themselves against potential misuse of their information,” the statement added.
According to the Washington Post the most recent attack comes less than a year after Trump International Hotels Management failed to notify customers of a data breach, which led to more than 70,000 credit card numbers and 300 Social Security numbers being exposed. The company had to pay $50,000 in penalties to the state of New York for its failure to inform guests in a timely manner and agreed to update its security practices as a result of the settlement.
“Why are hackers targeting hotels? Well, because they’re a good target,” Peter W. Singer, a senior fellow at the New America Foundation, told the Washington Post. “Then you look at Trump’s hotels, and they’re obviously a highly symbolic target.”
Justin Cappos, an associate professor of systems and security at New York University, told the Post that it “seems very negligent that this could happen a number of times,” adding, “These patterns of oversight are a huge problem.”
The Post additionally pointed to a ProPublica investigation that found numerous inefficiencies in the wireless networks of several of Trump’s properties, including his prized Mar-a-Lago resort.
“We could have hacked them in less than five minutes, but we refrained,” ProPublica reported.
Of his other properties ProPublica said it found “weak and open Wi-Fi networks, wireless printers without passwords, servers with outdated and vulnerable software and unencrypted login pages to backend databases containing sensitive information.”
Trump organization spokeswoman Amanda Miller told ProPublica in May that it follows security best practices but would not comment on specific measures. “Like virtually every other company these days, we are routinely targeted by cyber terrorists whose only focus is to inflict harm on great American businesses,” Miller said, ProPublica reported.